Secure Your Future with Unmatched Penetration Testing Expertise
Empower your organization with comprehensive penetration testing services offered by [Your Company Name]. Safeguard your systems, applications, and data against evolving cyber threats through proactive security assessments. Mitigate risks, enhance your security posture, and gain peace of mind knowing that your organization is fortified against potential attacks.
Contact us today to discuss your penetration testing requirements and discover how our expert services can help protect your organization from cyber threats. Secure your infrastructure, fortify your defenses, and stay one step ahead with FCS.
In a digital landscape fraught with evolving cyber threats, proactive security measures are paramount. With our comprehensive penetration testing services, [Your Company Name] empowers your organization to identify vulnerabilities, fortify defenses, and stay one step ahead of potential attacks.
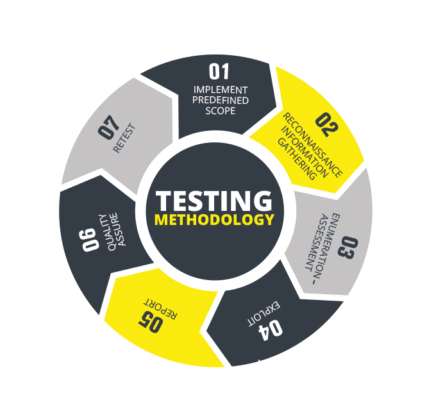
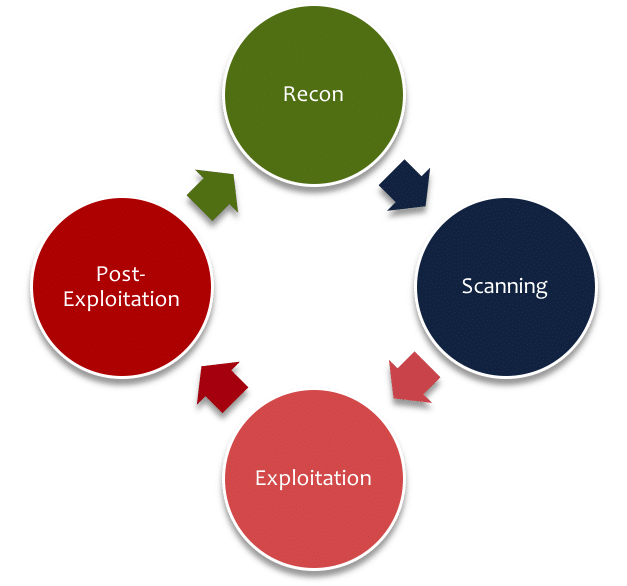
Our expert team of penetration testers combines industry-leading techniques, cutting-edge tools, and extensive experience to deliver holistic security assessments. By thoroughly evaluating your systems, applications, and digital assets, we provide actionable insights to mitigate risks and enhance your security posture.
Mitigate the ever-present risks that can compromise your sensitive data, disrupt operations, and damage your reputation. Our penetration testing reports offer clear, concise recommendations to address vulnerabilities effectively, enabling you to bolster your security controls and demonstrate compliance.